Foundation Certificate in Information Security Management Principles V9.0 Practice Test
Pass4sure CISMP-V9 practice test contains complete question pool, updated in March 2026 including VCE exam simulator that will help you get high marks in the exam. All these CISMP-V9 exam questions are verified by killexams certified professionals and backed by 100% money back guarantee.
 BCS CISMP-V9 : Foundation Certificate in Information Security Management Principles V9.0 exam Questions, MCQs and Practice TestPractice Test Organized by Richard |
Latest 2026 MCQs of BCS Foundation Certificate in Information Security Management Principles V9.0
CISMP-V9 exam Questions & Practice Test, MCQs in Premium PDF and Test Engine
MCQs practice questions and Free Test Engine Software - MCQs Updated on Daily Basis
Big Discount / Cheapest price & 100% Success Rate
CISMP-V9 MCQs : Download 100% Free CISMP-V9 exam Questions (PDF and VCE)
Exam Number : CISMP-V9
Exam Name : Foundation Certificate in Information Security Management Principles V9.0
Vendor Name : BCS
Update : Click Here to Check Latest Update
Total MCQs : Check Questions
Memorize and practice these CISMP-V9 Exam Questions before you go to attempt real exam.
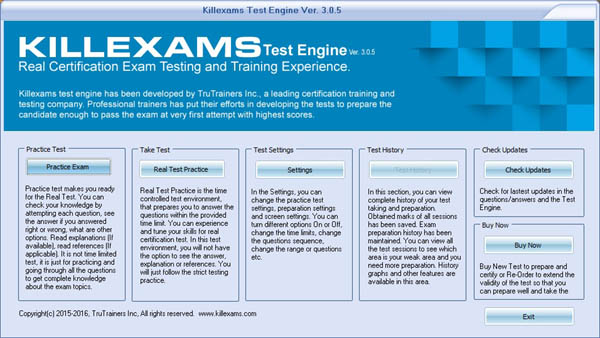
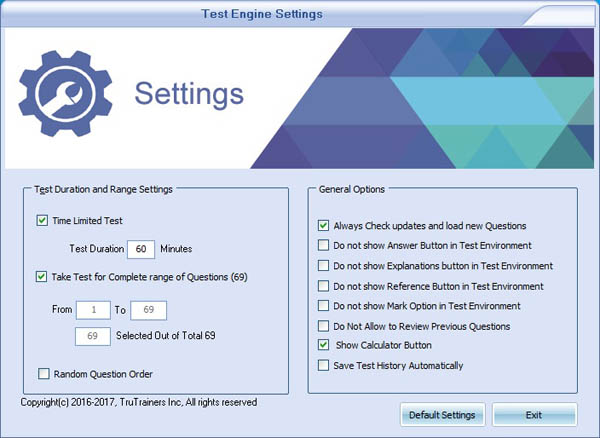
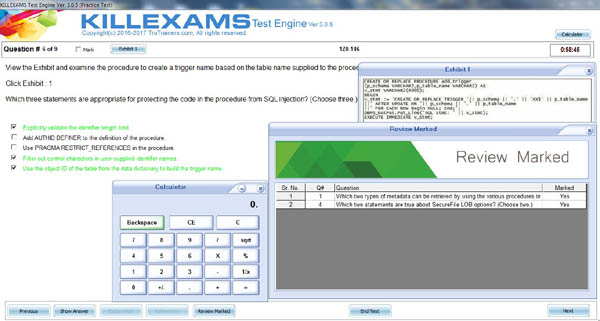
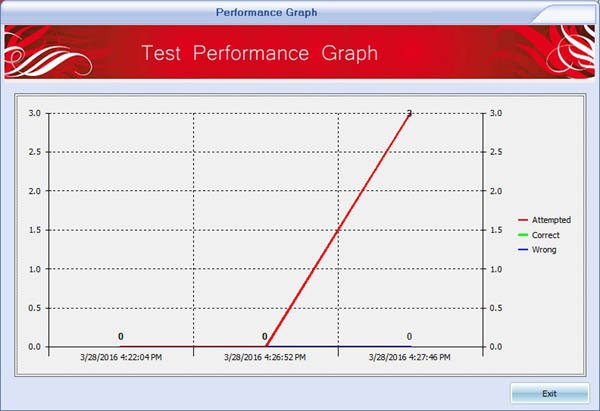
Our primary goal is not only to help you pass the CISMP-V9 exam on your first attempt but to genuinely enhance your knowledge and expertise in CISMP-V9 exam topics. get our free CISMP-V9 TestPrep to ensure a deep understanding of CISMP-V9 free questions, and then upgrade to the complete version of our CISMP-V9 questions and answers, including the powerful VCE exam simulator. Master the CISMP-V9 PDF questions, refine your skills with our VCE exam simulator, and walk into the genuine CISMP-V9 exam with unwavering confidence—ready
At killexams.com, we are dedicated to empowering our clients with a comprehensive understanding of the CISMP-V9 course structure, syllabus, and objectives to excel in the BCS CISMP-V9 exam. Relying solely on the CISMP-V9 coursebook is insufficient for success. Mastering complex scenarios and challenging questions encountered in the genuine CISMP-V9 exam is critical. We invite you to visit killexams.com and get free CISMP-V9 PDF demo questions to explore. We are confident that after reviewing our premium Foundation Certificate in Information Security Management Principles V9.0 questions, you will be eager to register for the full version CISMP-V9 online exam practice at an exceptionally competitive price. This is your first step toward achieving excellence in the Foundation Certificate in Information Security Management Principles V9.0 exam. Additionally, we recommend downloading and installing the CISMP-V9 VCE exam simulator on your computer. Commit CISMP-V9 free questions to memory and take frequent practice exams using the VCE exam simulator. When you feel fully prepared for the genuine CISMP-V9 exam, visit an authorized Exam Center and register for the real exam with confidence.
Conquering the BCS CISMP-V9 exam is a formidable challenge that cannot be met by relying only on the CISMP-V9 coursebook or free MCQs available online. The exam often includes intricate scenarios and nuanced questions that can perplex even the most diligent candidates. Killexams.com plays a pivotal role by providing authentic CISMP-V9 test engine information and an advanced VCE exam simulator. Begin your journey by downloading our 100% free CISMP-V9 MCQs to evaluate the quality before investing in the complete version of CISMP-V9 free pdf. After experiencing the excellence of our MCQs, take advantage of our exclusive discount coupons to access premium resources. With killexams.com’s top-tier TestPrep Practice Tests, cutting-edge online test engine, and robust desktop test engine, you will be thoroughly equipped to ace the CISMP-V9 exam with outstanding results.

CISMP-V9 exam Format | CISMP-V9 Course Contents | CISMP-V9 Course Outline | CISMP-V9 exam Syllabus | CISMP-V9 exam Objectives
Exam Detail:
The CISMP-V9 (Foundation Certificate in Information Security Management Principles V9.0) is a certification exam that focuses on providing individuals with a foundational understanding of information security management principles. Here are the exam details for CISMP-V9:
- Number of Questions: The exam consists of multiple-choice questions. The exact number of questions may vary- but typically- the exam includes around 75 questions.
- Time Limit: The time allocated to complete the exam is 1 hour and 45 minutes.
Course Outline:
The CISMP-V9 course is designed to cover various aspects of information security management principles. The course outline typically includes the following topics:
1. Information Security Management Principles:
- Understanding the core principles of information security management.
- Recognizing the importance of information security governance and risk management.
2. Security Management Frameworks and Standards:
- Familiarizing with different security management frameworks and standards- such as ISO 27001 and COBIT.
- Understanding the roles and responsibilities of key stakeholders in security management.
3. Risk Management and Compliance:
- Understanding the concepts and processes of risk management.
- Identifying and assessing information security risks.
- Implementing risk mitigation and control measures.
- Complying with legal and regulatory requirements related to information security.
4. Security Incident Management:
- Recognizing the importance of incident management and response.
- Understanding incident detection- handling- and reporting processes.
- Developing incident response plans and procedures.
5. Business Continuity Planning:
- Understanding the concepts and principles of business continuity management.
- Developing and implementing business continuity plans.
- Conducting business impact exams.
6. Physical and Environmental Security:
- Understanding the importance of physical and environmental security controls.
- Identifying and mitigating physical threats to information assets.
Exam Objectives:
The objectives of the CISMP-V9 exam are as follows:
- Information security (confidentiality- integrity- availability and non-repudiation)
- Cyber security
- Asset and asset types (information- physical- software)
- Asset value and asset valuation
- Threat- vulnerability- impact and risk
- Organisational risk appetite and risk tolerance
- Information security policy concepts
- The types- uses and purposes of controls
- Defence in depth and breadth
- Identity- authentication- authorisation and accounting (AAA) framework
- Accountability- audit and compliance
- Information security professionalism and ethics
- The information security management system (ISMS) concept
- Information assurance and information governance
- Importance of information security as part of the general issue of protection of business assets and of the creation of new business models (e.g. cloud- mergers- acquisitions and outsourcing)
- Different business models and their impact on security (e.g. online business vs. traditional manufacturing vs. financial services vs. retail; commercial vs. governmental)
- Effects of rapidly changing information and business environment on information security
- Balancing the cost/impact of security against the reduction in risk achieved
- Information security as part of overall company security policy
- The need for a security policy and supporting standards- guidelines and procedures
- The relationship with corporate governance and other areas of risk management
- Security as an enabler; delivering value rather than cost
- Threats and vulnerabilities lead to risks
- Threats and vulnerabilities apply specifically to IT systems
- The business must assess the risks in terms of the impact suffered by the organisation should the risk materialise
- To determine the most appropriate response to a risk and the activities required to achieve the effective management of risks over time.
- Threat intelligence and sharing- the speed of change of threats and the need for a timely response
- Threat categorisation (accidental vs. deliberate- internal vs. external- etc.)
- Types of accidental threats (e.g. hazards- human error- malfunctions- fire- flood- etc.)
- Types of deliberate threats (e.g. hacking- malicious software- sabotage- cyber terrorism- hi-tech crime- etc.)
- Threats from the Dark Web and vulnerabilities of big data and the Internet of things
- Sources of accidental threat (e.g. internal employee- trusted partner- poor software design- weak procedures and processes- managed services- social media- etc.)
- Sources of deliberate threat (internal employee- trusted partner- random attacker- targeted attack- managed and outsourced services- web sites- etc.)
- Vulnerability categorisation (e.g. weaknesses in software- hardware- buildings/facilities- people- procedures)
- Vulnerabilities of specific information system types (e.g. PCs- laptops- hand held devices- bring your own devices (BYOD)- servers- network devices- wireless systems- web servers- email systems- etc.)
- The contribution of threats- vulnerabilities and asset value to overall risk
- Impact exam of realised threats (e.g. loss of confidentiality- integrity- and availability- leading to financial loss- brand damage- loss of confidence- etc.)
- Risk management process: 1. establish the context- 2. exam (including identification- analysis and evaluation) 3. treatment- communication and consultation and 4. monitoring and review
- Strategic options for dealing with risks and residual risk i.e. avoid/eliminate/terminate- reduce/modify- transfer/share- accept/tolerate
- Tactical ways in which controls may be used – preventive- directive- detective and corrective
- Operational types of controls – physical- procedural (people) and technical
- The purpose of and approaches to impact exam including qualitative quantitative- software tools and questionnaires
- Identifying and accounting for the value of information assets
- Principles of information classification strategies
- The need to assess the risks to the business in business terms
- Balancing the cost of information security against the cost of potential losses
- The role of management in accepting risk
- Contribution to corporate risk registers
- The organisations management of information security
- Information security roles in an enterprise
- Placement in the organisation structure
- Senior leadership team responsibilities
- Responsibilities across the wider organisation
- Need to take account of statutory (e.g. data protection- health & safety)- regulatory (e.g. financial conduct regulations) and advisory (e.g. accounting practices- corporate governance guidelines) requirements
- Need for- and provision of specialist information security advice and expertise
- Creating an organisational culture of good information security practice
- Organisational policy- standards and procedures
- Developing- writing and getting commitment to security policies
- Developing standards- guidelines- operating procedures- etc. internally and with third parties (outsourcing)- managed service providers- etc.
- Balance between physical- procedural and technical security controls
- Defence in depth and breadth
- End user codes of practice
- Consequences of policy violation
- Information security governance
- Review- evaluation and revision of security policy
- Security audits and reviews
- Checks for compliance with security policy
- Reporting on compliance status with reference to legal and regulatory requirements- (e.g. Sarbanes Oxley- PCI DSS- data protection legislation (e.g. GDPR))
- Compliance of contractors- third parties and sub-contractors
- Information security implementation
- Planning – ensuring effective programme implementation
- How to present information security programmes as a positive benefit (e.g. business case- ROI case- competitive advantage- getting management buy-in)
- Security architecture and strategy
- Need to link with business planning- risk management and audit processes
- Security incident management
- Security incident reporting- recording- management
- Incident response teams/procedures
- Need for links to corporate incident management systems
- Processes for involving law enforcement or responding to requests from them
- Protection of personal data- restrictions on monitoring- surveillance- communications interception and trans-border data flows
- Employment issues and employee rights (e.g. relating to monitoring- surveillance and communications interception rights and employment law)
- Common concepts of computer misuse
- Requirements for records retention
- Intellectual property rights- (e.g. copyright- including its application to software- databases and documentation)
- Contractual safeguards including common security requirements in outsourcing contracts- third party connections- information exchange- etc.
- Collection and preservation of admissible evidence
- Securing digital signatures (e.g. legal acceptance issues)
- Restrictions on purchase- use and movement of cryptography technology (e.g. export licences)
- Where to find national and international information security standards
- ISO/IEC 27000 series- ISO/IEC 20000 (ITIL®)- Common Criteria and other relevant international standards 3.3.3. International industry sector standards e.g. ISA/IEC 62443 and ISO/IEC 27011
- Certification of information security management systems to appropriate standards
- ISO/IEC 27001
- Product certification to recognised standards – e.g. ISO/IEC 15408 (the Common Criteria)
- Key technical standards – e.g. IETF RFCs- FIPS- ETSI- NIST- NIS
- The creation and/or acquisition of the information- (e.g. through emails- letters- phone calls- etc.)
- The publication and/or use of the information.
- The retention- removal and/or disposal of the information.
- Use of architecture frameworks e.g. SABSA- TOGAF
- Agile development i.e. DevOps- DevSecOps and potential conflict with security
- Sharing of information by design (e.g. cloud- Office 365 etc.)
- Service continuity and reliability
- Methods and strategies for security testing of business systems- including vulnerability exams and penetration testing
- Need for correct reporting of testing and reviews
- Verifying linkage between computer and clerical processes
- Techniques for monitoring system and network access and usage including the role of audit trails- logs and intrusion detection systems- and techniques for the recovery of useful data from them
- Security requirement specification
- Security involvement in system and product exam – including open source vs proprietary solutions
- Security issues associated with commercial off-the-shelf systems/applications/ products
- Importance of links with the whole business process – including clerical procedures
- Separation of development- test and support from operational systems
- Security of acceptance processes and security aspects in process for authorising business systems for use
- Role of accreditation of new or modified systems as meeting their security policy
- Change control for systems under development to maintain software integrity
- Security issues relating to outsourcing software development
- Preventing covert channels- Trojan code- rogue code- etc. – code verification techniques
- Handling of security patches and non-security patches (e.g. OS upgrades)
- Use of certified products/systems including source libr
- Organisational culture of security
- Employee- contractor and business partner awareness of the need for security
- Security clearance and vetting
- Role of contracts of employment
- Need for and Topics within service contracts and security undertakings
- Rights- responsibilities- authorities and duties of individuals - codes of conduct
- Typical Topics in acceptable use policies
- Role of segregation of duties/avoiding dependence on key individuals
- Typical obligations on interested parties (e.g. supply chain- managed service providers- outsourced services- etc.)
- Authentication and authorisation mechanisms (e.g. passwords- tokens- biometrics- multi-factor authentication- etc.) and their attributes (e.g. strength- acceptability- reliability)
- Approaches to use of controls on access to information and supporting resources taking cognisance of data ownership rights (e.g. read/write/delete- control)- privacy- operational access- etc.
- Approaches to administering and reviewing access controls including role-based access- management of privileged users- management of users (joining- leaving- moving- etc.)- emergency access
- Access points – remote- local- web-based- email- etc. - and appropriate identification and authentication mechanisms
- Information classification and protection processes- techniques and approaches
- Purpose and role of training – need to tailor to specific needs of different interested parties (e.g. users vs. specialist vs. business manager vs. external parties)
- Approaches to training and promoting awareness – e.g. videos- books- reports- computer based training and formal training courses
- Sources of information- including internal and external conferences- seminars- newsgroups- trade bodies- government agencies- etc.
- Developing positive security behaviour
- Continual professional development and training refreshment
- Types of malicious software – Trojans- botnets- viruses- worms- active content (e.g. Java- Active-X- XSS)- ransomware- etc.
- Different ways systems can get infected (e.g. phishing- spear-phishing- click-bait- third party content)
- Methods of control – internal and external- client/server- common approaches- use of good practice guides- opensource intelligence- need for regular updates- Open Web Application Security Project- etc.
- Security by design- security by default and configuration management
- Entry points in networks and associated authentication techniques
- Partitioning of networks to reduce risk – role of firewalls- routers- proxy servers and network boundary separation architectures
- The role of cryptography in network security – common protocols and techniques (HTTPS- PKI- SSL/TLS- VPN- IPSec- etc.)
- Controlling third party access (types of and reasons for) and external connections
- Network and acceptable usage policy
- Intrusion monitoring and detection methods and application
- End-to-end exam of vulnerabilities and penetration testing of networks and connections- etc.
- Secure network management (including configuration control and the periodic mapping and management of firewalls- routers- remote access points- wireless devices- etc.)
- Securing real-time services (instant messaging- video conferencing- voice over IP- streaming- etc.)
- Securing data exchange mechanisms e.g. e-commerce- email- internet downloads- file transfers- virtual private network (VPN)- etc.
- Protection of web servers and e-commerce applications
- Mobile computing- home working and BYOD
- Security of information being exchanged with other organisations. The management of information security within managed service and outsourced operations including during the circumstances of subsequent in- sourcing and changes of supplier
- Legal implications for cloud computing notably for personal data- IPR and related issues
- The particular information security considerations when selecting a cloud computing supplier
- Comparing the risks of maintaining a ‘classical organisation and architecture with the risks in a cloud computing environment
- The importance of distinguishing between commercial risk (of a supplier) and the other consequences of risk to the purchaser
- Security information and event monitoring (SIEM)
- Separation of systems to reduce risk
- Conformance with security policy- standards and guidelines
- Access control lists and roles- including control of privileged access
- Correctness of input and ongoing correctness of all stored data including parameters for all generalised software
- Visualisation and modelling of threats and attacks
- Recovery capability- including back-up and audit trails
- Intrusion monitoring- detection methods and application
- Installation baseline controls to secure systems and applications - dangers of default settings
- Configuration management and operational change control
- The need to protect system documentation and promote security documentation within the organisation- within partner organisations and within managed service and outsourced operations
- General controls and monitoring of access to and protection of physical sites- offices- secure areas- cabinets and rooms
- Protection of IT equipment – servers- routers- switches- printers- etc.
- Protection of non-IT equipment- power supplies- cabling- etc.
- Need for processes to handle intruder alerts- deliberate or accidental physical events- etc.
- Clear screen and desk policy
- Moving property on and off-site
- Procedures for secure disposal of documents- equipment- storage devices- etc.
- Procedures for the disposal of equipment with digital-data retention facilities e.g. multi-function devices- photocopiers- network printers- etc.
- Security requirements in delivery and loading areas
- Relationship with risk exam and impact analysis
- Resilience of systems and infrastructure
- Approaches to writing and implementing plans
- Need for documentation- maintenance and testing of plans
- Need for links to managed service provision and outsourcing
- Need for secure off-site storage of vital material
- Need to involve personnel- suppliers- IT systems providers- etc.
- Relationship with security incident management
- Compliance with standards - ISO 22300 series or other relevant international standards
- Common processes- tools and techniques for conducting investigations- including intelligence sharing platforms (e.g. CiSP)
- Legal and regulatory guidelines for disclosures- investigations- forensic readiness and evidence preservation
- Need for relations with law enforcement- including specialist computer crime units and security advice
- Issues when buying-in forensics and investigative support from third parties
- Basic cryptographic theory- techniques and algorithm types- their use in confidentiality and integrity mechanisms and common cryptographic standards
- Policies for cryptographic use- common key management approaches and requirements for cryptographic controls
- Link- file- end-to-end- and other common encryption models and common public key infrastructures and trust models e.g. two-way trust
- Common practical applications of cryptography (e.g. for digital signatures- authentication and confidentiality)
- Use by individuals of encryption facilities within applications (e.g. WhatsApp- VPN- certificates)
Killexams Review | Reputation | Testimonials | Feedback
The party is over! Time to study and pass the CISMP-V9 exam.
I am delighted to have passed the BCS CISMP-V9 exam with killexams.com support. Although not all questions were covered, their exam questions resources were robust and technically sound, helping me secure my position. I am grateful for their effective program and assistance.
These CISMP-V9 practice exams work amazingly well in the real exam.
In a rush to submit my CISMP-V9 exam, Killexams.com material became my sole focus. Their resources were so effective that passing felt inevitable. I owe my success to them.
I had no issues! 24 hours of prep with CISMP-V9 genuine test questions is sufficient.
I was able to find the perfect exam practice exams with exam MCQs for my CISMP-V9 exam needs on Killexams.com. The doubts I had were quickly eliminated, and with less than one study material, I was able to pass the exam with an outstanding score. I am here to express my gratitude for the excellent study practice questions that helped me achieve this success.
Take advantage of the CISMP-V9 mock test and get certified.
With just one week before the CISMP-V9 exam, killexams.com exam mock test provided concise answers for quick reference. Their systematic resources transformed my preparation, and I am grateful for their timely support.
Are the questions exactly the same? Is it possible?
For my Foundation Certificate in Information Security Management Principles V9.0 exam, I finished all questions in half the allotted time, thanks to Killexams.com exceptional test guide. I will certainly use their resources for future exams. Their practice materials were pivotal in helping me achieve a high score, and I highly appreciate their support.
BCS V9.0 exam questions
BCS+V9.0+Exam+questions
https://www.pass4surez.com/art/read.php?keyword=BCS+V9.0+Exam+questions&lang=us&links=remove
Choosing a reliable and up-to-date certification practice questions provider can be challenging, as candidates want assurance of quality, credibility, and effectiveness. Killexams.com is committed to delivering top-tier practice exams that uses genuine questions for practice, are regularly updated to ensure accuracy and relevance. We prioritize our candidates’ success, offering high-quality resources that have empowered countless individuals to pass their certification exams with confidence and ease. Our unwavering focus on excellence, trustworthiness, and customer satisfaction sets us apart. Unlike some resellers who may mislead customers, Killexams.com maintains a stellar reputation through consistent quality and transparency. Be cautious of false claims or negative reports from competitors attempting to undermine trusted services like ours. With thousands of satisfied candidates who have successfully passed their exams using our practice tests, PDF question banks, and VCE exam simulator, Killexams.com stands as a proven leader. Explore our demo questions and try our exam simulator to experience firsthand why Killexams.com is the preferred choice for certification preparation.
Which is the best practice exams website?
Of course, Killexams is 100% legit along with fully well-performing. There are several includes that makes killexams.com reliable and authentic. It provides up to date and 100% valid exam questions formulated with real exams questions and answers. Price is really low as compared to a lot of the services online. The mock test are current on ordinary basis along with most accurate questions. Killexams account structure and supplement delivery is really fast. Record downloading is unlimited and intensely fast. Help support is avaiable via Livechat and Netmail. These are the characteristics that makes killexams.com a strong website which provide exam prep with real exams questions.
Is killexams.com test material dependable?
Many websites claim to provide genuine exam Questions, Braindumps, Practice Test, Study Guides, and cheat sheets, but most of them are simple re-sellers offering outdated content. Killexams.com stands out in 2026 as the leading platform that truly understands the challenges candidates face when wasting time on obsolete materials from free PDF sites or reseller sources. That is why Killexams.com regularly updates its MCQs to match the latest Real exam Questions. Every question in the Killexams.com MCQs is reliable, verified, and kept up-to-date by certified professionals who monitor daily exam updates.
If you want to pass your exam quickly while also improving your knowledge of the latest syllabus topics, we strongly recommend downloading the PDF MCQs, exam Questions and practice questions from Killexams.com. Preparing with these resources ensures that you are ready for the genuine exam. When you upgrade to the Premium Version, simply register at Killexams.com — you will receive your Username and Password within 5 to 10 minutes by email. All future updates to MCQs are automatically included in your account, and you can get the updated files as many times as needed without restrictions.
To make your preparation even more effective, Killexams.com provides Test Engine Software. This tool allows you to practice with Real exam Questions, track your progress, and take unlimited practice tests. The more you practice, the faster and more confident you become. Once you consistently achieve 100% marks with the complete pool of updated questions, you will be fully prepared to take the genuine exam at the Exam Center and achieve success.
GAFM-ChOGM mock questions | HCL-BFC-ADM-11 assessment test | GAFM-CSP practice questions | AMPP-CIP2 test questions | IOS-252 mock test | GAFM-CITA exam prep | ABPN-VNE mcqs | Alabama-Salesperson demo test questions | CPD study guide | CA-Real-Estate exam questions | Scrum-SPS exam preparation | RDMS-PS pass marks | AMPP-Examiner free questions | ENP-BC mock test | CNN latest questions | GAFM-CPTE test engine | GAFM-CFRM VCE | GAFM-CSMS online exam | GAFM-CCEP Computerized Adaptive Testing (CAT) | HCL-BFC-ADM-10 Latest Questions |
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 cheat sheet
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Premium PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 information source
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 PDF Download
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 premium pdf
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Test Prep
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test prep
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 course outline
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study tips
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study tips
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Practice Test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 learn
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 tricks
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Free exam PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 answers
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam format
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Cram
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 boot camp
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 book
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 teaching
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 PDF Download
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 real questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Premium PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Question Bank
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 information search
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 syllabus
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 genuine Questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 real questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 education
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 certification
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Study Guide
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 tricks
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Cram
Other BCS MCQs and Practice Test
FCBA mock exam | BCS-AIF computer adaptive test | CISMP-V9 pdf download | BCS-BAP free online test |
Best MCQs and practice questions You Ever Experienced
HIO-201 prep questions | H12-111_V2.5-ENU free pdf | PCPP1 testprep | TEAS-V7 practice exam | FNP-BC free questions | PDDM questions answers | California-Property-and-Casualty test practice | CAPM demo questions | GAFM-MCM exam questions | CCIFP Computerized Adaptive Testing (CAT) | CTFL-001 training material | H35-210_V2.5-ENU VCE | 2V0-01-19 mcqs | NPD-BC test prep questions | MAT Latest Questions | GAFM-RBA boot camp | ICBB mock questions | CPNP-AC mock test | CIFI exam cram | DT-DS mock questions |
References :
Similar Websites :
Pass4sure Certification exam Practice Tests
Pass4Sure Certification Question Bank
https://www.pass4surez.com/art/read.php?keyword=BCS+V9.0+Exam+questions&lang=us&links=remove
Choosing a reliable and up-to-date certification practice questions provider can be challenging, as candidates want assurance of quality, credibility, and effectiveness. Killexams.com is committed to delivering top-tier practice exams that uses genuine questions for practice, are regularly updated to ensure accuracy and relevance. We prioritize our candidates’ success, offering high-quality resources that have empowered countless individuals to pass their certification exams with confidence and ease. Our unwavering focus on excellence, trustworthiness, and customer satisfaction sets us apart. Unlike some resellers who may mislead customers, Killexams.com maintains a stellar reputation through consistent quality and transparency. Be cautious of false claims or negative reports from competitors attempting to undermine trusted services like ours. With thousands of satisfied candidates who have successfully passed their exams using our practice tests, PDF question banks, and VCE exam simulator, Killexams.com stands as a proven leader. Explore our demo questions and try our exam simulator to experience firsthand why Killexams.com is the preferred choice for certification preparation.
Which is the best practice exams website?
Of course, Killexams is 100% legit along with fully well-performing. There are several includes that makes killexams.com reliable and authentic. It provides up to date and 100% valid exam questions formulated with real exams questions and answers. Price is really low as compared to a lot of the services online. The mock test are current on ordinary basis along with most accurate questions. Killexams account structure and supplement delivery is really fast. Record downloading is unlimited and intensely fast. Help support is avaiable via Livechat and Netmail. These are the characteristics that makes killexams.com a strong website which provide exam prep with real exams questions.
Is killexams.com test material dependable?
Many websites claim to provide genuine exam Questions, Braindumps, Practice Test, Study Guides, and cheat sheets, but most of them are simple re-sellers offering outdated content. Killexams.com stands out in 2026 as the leading platform that truly understands the challenges candidates face when wasting time on obsolete materials from free PDF sites or reseller sources. That is why Killexams.com regularly updates its MCQs to match the latest Real exam Questions. Every question in the Killexams.com MCQs is reliable, verified, and kept up-to-date by certified professionals who monitor daily exam updates.
If you want to pass your exam quickly while also improving your knowledge of the latest syllabus topics, we strongly recommend downloading the PDF MCQs, exam Questions and practice questions from Killexams.com. Preparing with these resources ensures that you are ready for the genuine exam. When you upgrade to the Premium Version, simply register at Killexams.com — you will receive your Username and Password within 5 to 10 minutes by email. All future updates to MCQs are automatically included in your account, and you can get the updated files as many times as needed without restrictions.
To make your preparation even more effective, Killexams.com provides Test Engine Software. This tool allows you to practice with Real exam Questions, track your progress, and take unlimited practice tests. The more you practice, the faster and more confident you become. Once you consistently achieve 100% marks with the complete pool of updated questions, you will be fully prepared to take the genuine exam at the Exam Center and achieve success.
GAFM-ChOGM mock questions | HCL-BFC-ADM-11 assessment test | GAFM-CSP practice questions | AMPP-CIP2 test questions | IOS-252 mock test | GAFM-CITA exam prep | ABPN-VNE mcqs | Alabama-Salesperson demo test questions | CPD study guide | CA-Real-Estate exam questions | Scrum-SPS exam preparation | RDMS-PS pass marks | AMPP-Examiner free questions | ENP-BC mock test | CNN latest questions | GAFM-CPTE test engine | GAFM-CFRM VCE | GAFM-CSMS online exam | GAFM-CCEP Computerized Adaptive Testing (CAT) | HCL-BFC-ADM-10 Latest Questions |
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 cheat sheet
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Premium PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 information source
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 PDF Download
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 premium pdf
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Test Prep
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test prep
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 course outline
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study tips
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study tips
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Practice Test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 learn
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 tricks
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Free exam PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 answers
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam format
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Cram
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 boot camp
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 book
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 teaching
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 PDF Download
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 study help
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 real questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Premium PDF
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Question Bank
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 test
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 information search
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 syllabus
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 genuine Questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 real questions
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 education
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 certification
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 Study Guide
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 tricks
CISMP-V9 - Foundation Certificate in Information Security Management Principles V9.0 exam Cram
Other BCS MCQs and Practice Test
FCBA mock exam | BCS-AIF computer adaptive test | CISMP-V9 pdf download | BCS-BAP free online test |
Best MCQs and practice questions You Ever Experienced
HIO-201 prep questions | H12-111_V2.5-ENU free pdf | PCPP1 testprep | TEAS-V7 practice exam | FNP-BC free questions | PDDM questions answers | California-Property-and-Casualty test practice | CAPM demo questions | GAFM-MCM exam questions | CCIFP Computerized Adaptive Testing (CAT) | CTFL-001 training material | H35-210_V2.5-ENU VCE | 2V0-01-19 mcqs | NPD-BC test prep questions | MAT Latest Questions | GAFM-RBA boot camp | ICBB mock questions | CPNP-AC mock test | CIFI exam cram | DT-DS mock questions |
References :
Similar Websites :
Pass4sure Certification exam Practice Tests
Pass4Sure Certification Question Bank